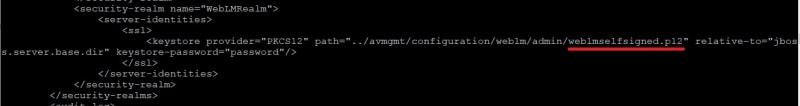
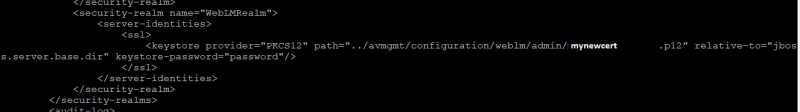
We have 3 duplex CM's that are located in Asia, Europe, and US from these we are deploying several survivable sites. The first was deployed along with the System Manager and uses the SMGR as its WebLM, all is ok there. The new Duplex's that are deployed in Asia and US have also had standalone WebLM deployed with them as each location has AAM which doesn't support centralized licensing. The problem I have is both AAM have License errors even though each WebLM has AAM Licenses loaded. I think it is probably a certificate issue (not sure). I did save the certificate from the WebLM browser and added it as a TM_INBOUND_TLS trusted certificate to the System Manager in the inventory as described in the WebLM deployment.
So far the AAM has been deployed with the 7.1 OVA and Patches added to SP2 and pr req CM patches were done. Added the SMGR CA certificate to the Trusted Certs and created an endpoint certificate in SMGR and put that in the server/application certificates.
So far the AAM has been deployed with the 7.1 OVA and Patches added to SP2 and pr req CM patches were done. Added the SMGR CA certificate to the Trusted Certs and created an endpoint certificate in SMGR and put that in the server/application certificates.